JWT Authentication in Node.js Explained Simply
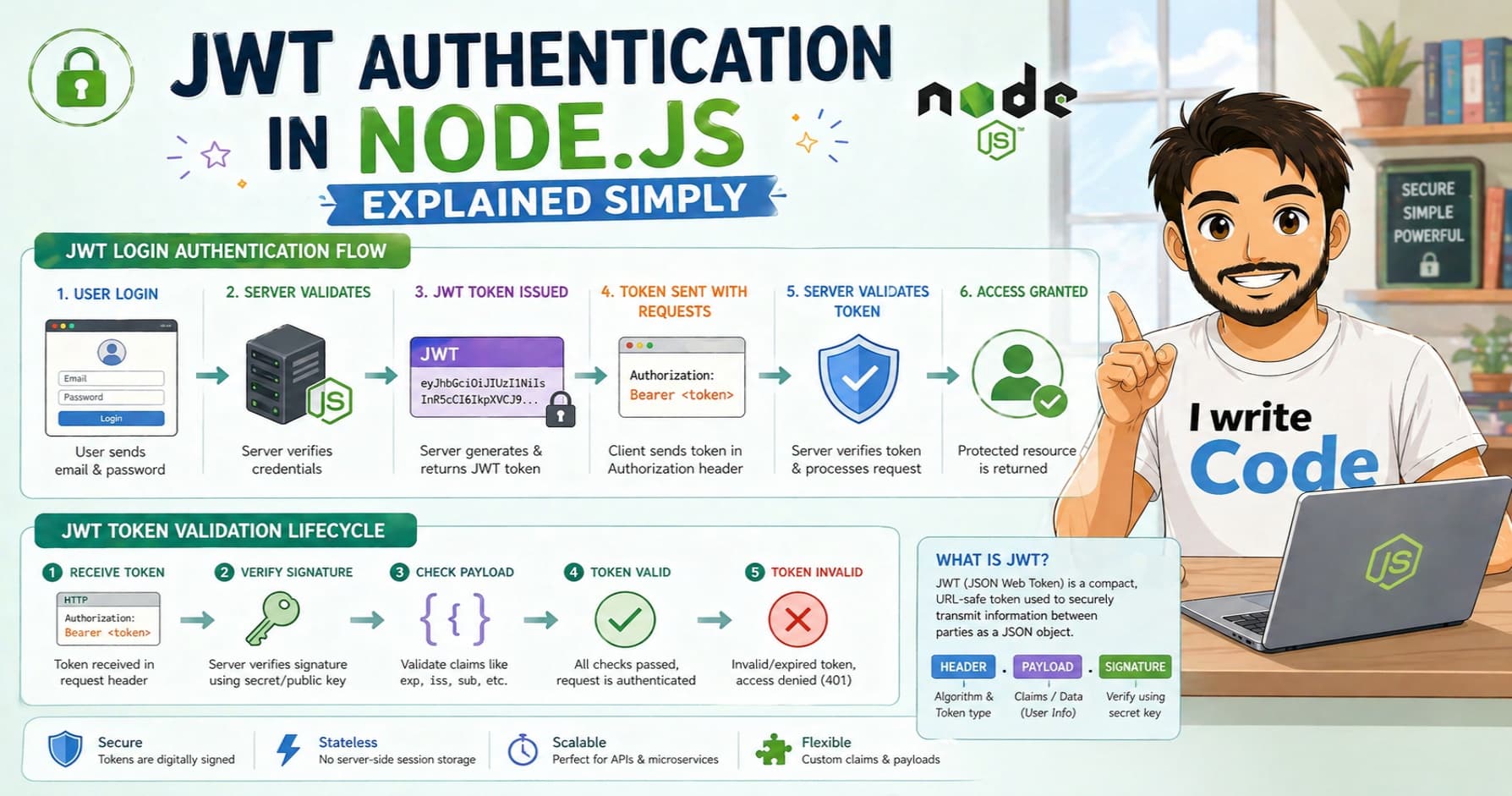
If you’ve ever built or used a modern web application, you’ve encountered the login screen countless times. Behind that simple username and password field lies a critical security process: authentication. In today’s API-driven world, one of the most popular and scalable ways to handle this is using JWTs, or JSON Web Tokens. They’re lightweight, stateless, and integrate seamlessly with Node.js backends. In this guide, we’ll break down what authentication means, what a JWT actually is, how it’s structured, and how to implement a secure login flow in Node.js, all explained for beginners.
What Authentication Means
Authentication is the process of verifying a user’s identity. When someone submits their credentials, the system checks whether they are who they claim to be. It’s crucial to distinguish authentication from authorization: authentication answers “Who are you?” while authorization answers “What are you allowed to do?”
Think of authentication as showing your ID at a building’s front desk. Authorization is the access badge that decides which floors you can visit once inside. Without reliable authentication, malicious actors could easily impersonate legitimate users. JWTs solve this by providing a secure, cryptographically verifiable way to confirm identity across multiple requests without storing session data on the server.
What is a JWT?
A JWT (pronounced “jot”) is a compact, URL-safe token that securely represents claims between two parties. Unlike traditional session-based authentication, which stores user state on the server or in a database, JWTs are stateless.
Here’s how it works: after a successful login, your server generates a JWT and sends it to the client. The client stores it and attaches it to every subsequent request. The server doesn’t need to query a session store; it simply verifies the token’s signature to trust the claims inside. This makes JWTs highly efficient for RESTful APIs, mobile apps, and microservice architectures where scaling and performance matter.
Structure of a JWT
A JWT isn’t a random string of characters. It’s composed of three distinct parts, separated by dots: header.payload.signature. Each part is Base64Url encoded, which is why tokens look like long, unreadable sequences.
Header
The header contains metadata about the token. It typically specifies the signing algorithm and the token type.
{
"alg": "HS256",
"typ": "JWT"
}
Payload
The payload holds the actual claims, statements about the user and token metadata. Common standard claims include sub (subject/user ID), iat (issued at), and exp (expiration time). You can also include custom data. For example:
{
"sub": "user_101",
"name": "Suprabhat", age: 23,
"role": "member",
"iat": 1715000000,
"exp": 1715003600
}
Important: Payloads are encoded, not encrypted. Anyone can decode them using online tools. Never store sensitive information like passwords, credit card numbers, or private keys in a JWT.
Signature
The signature is the security backbone of the token. It’s created by taking the encoded header and payload, combining them with a secret key known only to your server, and running them through the algorithm specified in the header (e.g., HMAC-SHA256). If an attacker modifies the header or payload, the signature will no longer match, and the server will immediately reject the token.
The JWT Login Flow
Let’s walk through how this works in practice using our example user: name: "Suprabhat", age: 23,.
Login Request: Suprabhat enters their email and password on the frontend and submits a
POSTrequest to your Node.js/api/loginendpoint.Credential Verification: Your server queries the database, hashes the submitted password, and compares it with the stored hash.
Token Generation: If the credentials match, the server generates a JWT. It includes a unique user identifier, sets an expiration time (e.g., 1 hour), and signs it with a secure secret key.
Response Delivery: The server sends the JWT back to the client, usually in the JSON response body or as a secure HTTP-only cookie.
Client Storage: The frontend securely stores the token (commonly in memory or
localStorage, depending on your security model).
From this point forward, Suprabhat won’t need to log in again until the token expires. The JWT acts as a temporary, cryptographically verified digital ID card.
Sending Tokens with Requests
Once the client holds the JWT, it must attach it to every request that requires authentication. The industry standard is using the Authorization HTTP header with the Bearer scheme:
GET /api/dashboard
Authorization: Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiJ1c2VyXzEwMSJ9...
Modern frontend frameworks handle this automatically. For example, using Axios, you can set up a request interceptor that reads the stored token and attaches it before every API call.
Security Tip: Never pass JWTs in URL query parameters. URLs are logged in browser history, server logs, and proxy caches, making tokens highly vulnerable to leakage.
Protecting Routes in Node.js
Now, let’s see how your Node.js server verifies incoming tokens. You’ll typically use the official jsonwebtoken package to build a reusable middleware function.
const jwt = require('jsonwebtoken');
const authenticateToken = (req, res, next) => {
const authHeader = req.headers['authorization'];
const token = authHeader && authHeader.split(' ')[1]; // Extracts "Bearer <token>"
if (!token) {
return res.status(401).json({ error: 'Authentication required' });
}
jwt.verify(token, process.env.JWT_SECRET, (err, user) => {
if (err) {
return res.status(403).json({ error: 'Invalid or expired token' });
}
req.user = user; // Attach decoded payload to the request object
next(); // Proceed to the actual route handler
});
};
// Apply middleware to protected routes
app.get('/api/profile', authenticateToken, (req, res) => {
res.json({ message: `Welcome, ${req.user.name}!` });
});
This middleware checks for the presence of a token, verifies its cryptographic signature, and ensures it hasn’t expired. If valid, it attaches the decoded payload to req.user, making user data available to your route handlers. If invalid, it short-circuits the request with a clear HTTP status code.
Conclusion
JWT authentication might sound intimidating at first, but it’s fundamentally just a secure, standardized way to pass verified user data between client and server. By understanding its three-part structure, mastering the login flow, and implementing clean verification middleware in Node.js, you can build scalable, stateless APIs with confidence.
Always follow security best practices: use strong, randomly generated secret keys, set reasonable token expiration times, implement token refresh strategies for longer sessions, and never expose sensitive data in the payload. With these foundations in place, you’re well-equipped to secure your next Node.js application like a pro.